A sophisticated phishing campaign has recently emerged, leveraging Google Cloud’s trusted infrastructure to host malicious redirects.
The campaign’s technical structure leverages Google Cloud Storage legitimate domain, googleapis.com, which is widely trusted by mail gateways and end users alike.
This provides the attackers an opportunity to bypass common security layers such as SPF and DKIM validation.
Investigations show that the attackers created a GCS bucket named “whilewait”, where they stored an HTML file called comessuccess.html.
Security researchers have identified more than 25 phishing emails targeting a single user account each ultimately directing victims to a deceptive link hosted on Google Cloud Storage (GCS).
The file acts as a redirector or gatekeeper, silently transferring users from the legitimate Google domain to an external phishing page.
Once redirected, the user lands on fraudulent payment or reward portals used for credit card harvesting or malware distribution.
This redirection technique makes detection difficult, as the initial link appears authentic and hosted by Google. Traditional email filters generally trust googleapis.com, giving these messages a much higher chance of landing in inboxes.
Expanding Social Engineering Themes
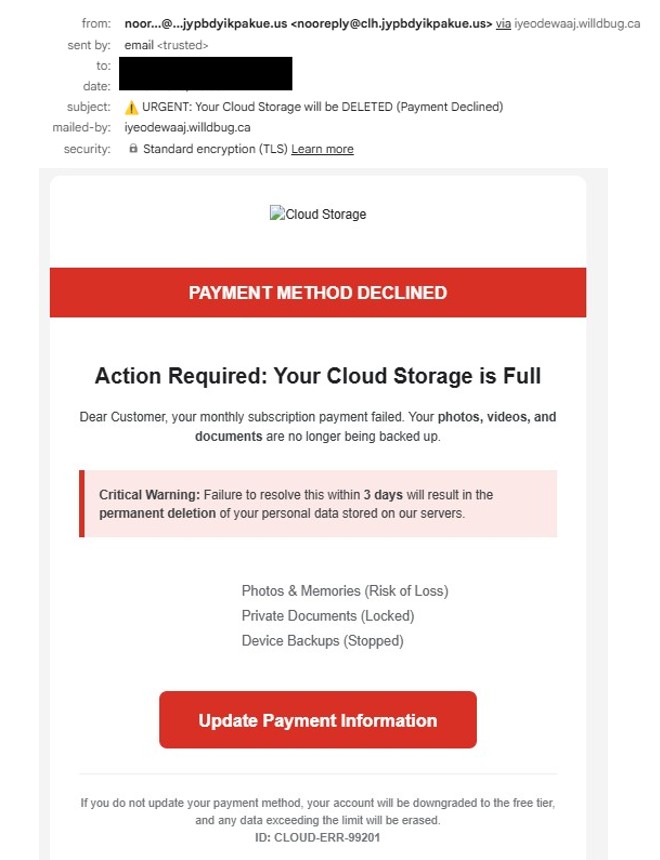
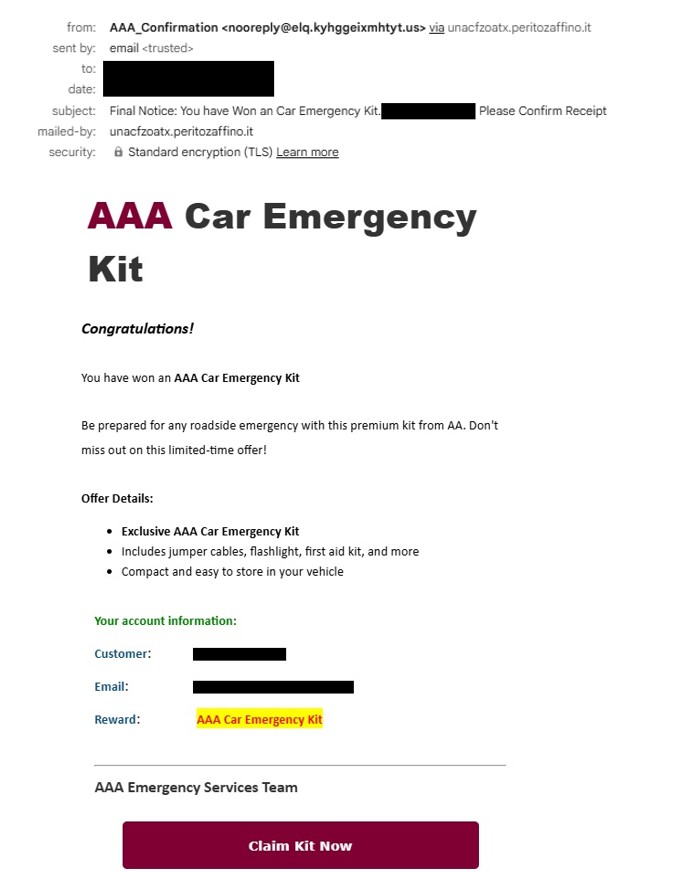
Analysis of over 25 captured samples revealed a wide array of social engineering themes, each crafted to exploit different emotional triggers. Despite the variations, all messages share a common technical path leading to the same malicious GCS bucket.
Common lures identified include:
- Account Urgency: “Google Account Storage Full” or “Backup Expired” alerts.
- Security Concerns: “Critical Threat Detected” notifications urging immediate action.
- Promotional Hooks: Fake offers from brands like Lowe’s, T-Mobile, and State Farm.
- Lifestyle Bait: Ads for “Homemade Recipes,” “Gift Baskets,” or “Health Remedies.”
These themes are designed to push recipients toward interaction clicks that lead directly into the GCS redirect chain.
By hosting the initial link on Google’s servers, the attackers ensure the email passes authentication checks like SPF and DKIM.
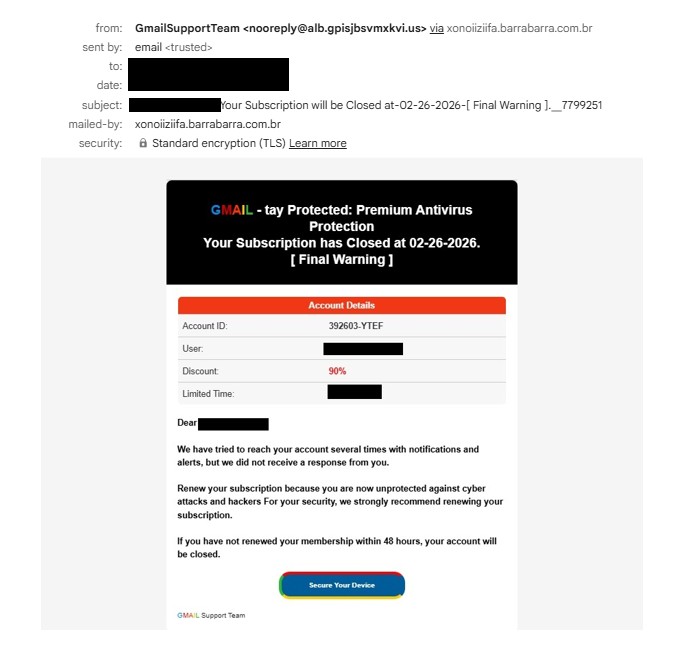
Once a victim clicks through the hosted Google redirector, they encounter a landing page requesting payment details for shipping, service updates, or account recovery.
This stage marks the attackers’ primary objective harvesting credit card information. The submitted financial details are instantly transmitted to the attacker-controlled backend systems, leading to unauthorized transactions or identity theft.
Researchers note that this type of “Trusted-Platform Phishing” increasingly relies on reputable cloud providers to camouflage malicious intent. The result is a convincing and resilient infrastructure that stays active longer than traditional phishing sites.
Defensive Measures
The goal remains consistent, drive traffic to the whilewait storage bucket to initiate a fraudulent transaction or steal sensitive information.
Security professionals recommend several countermeasures to mitigate similar campaigns:
- Inspect the Redirect Path: Verify the full URL chain before clicking. Links beginning with storage.googleapis.com may belong to third-party actors.
- Examine Sender Metadata: Look beyond display names. Many samples use random Gmail-like aliases with no association to legitimate brands.
- Report Abuse: Submit reports to the Google Cloud Abuse Team to turn off the malicious bucket and disrupt the phishing infrastructure.
This campaign highlights how trusted platforms can be weaponized to host malicious payloads reinforcing the need for both heightened user awareness and vigilant threat reporting across cloud environments.