Google and its partners have disrupted a major Chinese state-linked cyber espionage campaign that breached at least 53 telecommunications and government entities across 42 countries on four continents.
The operation, led by Google Threat Intelligence Group (GTIG) alongside Mandiant and industry partners, dismantled the infrastructure of a suspected People’s Republic of China (PRC) nexus group tracked as UNC2814, active since at least 2017.
UNC2814 has a long history of targeting governments and telecom operators worldwide, including regions in Africa, Asia, and the Americas. In this campaign, the group focused on large telecommunications providers and government organizations, enabling wide access to sensitive communications and personal data.
As of February 18 investigators confirmed 53 victims in 42 countries and suspected infections in at least 20 additional nations, highlighting the campaign’s global reach.
GRIDTIDE backdoor
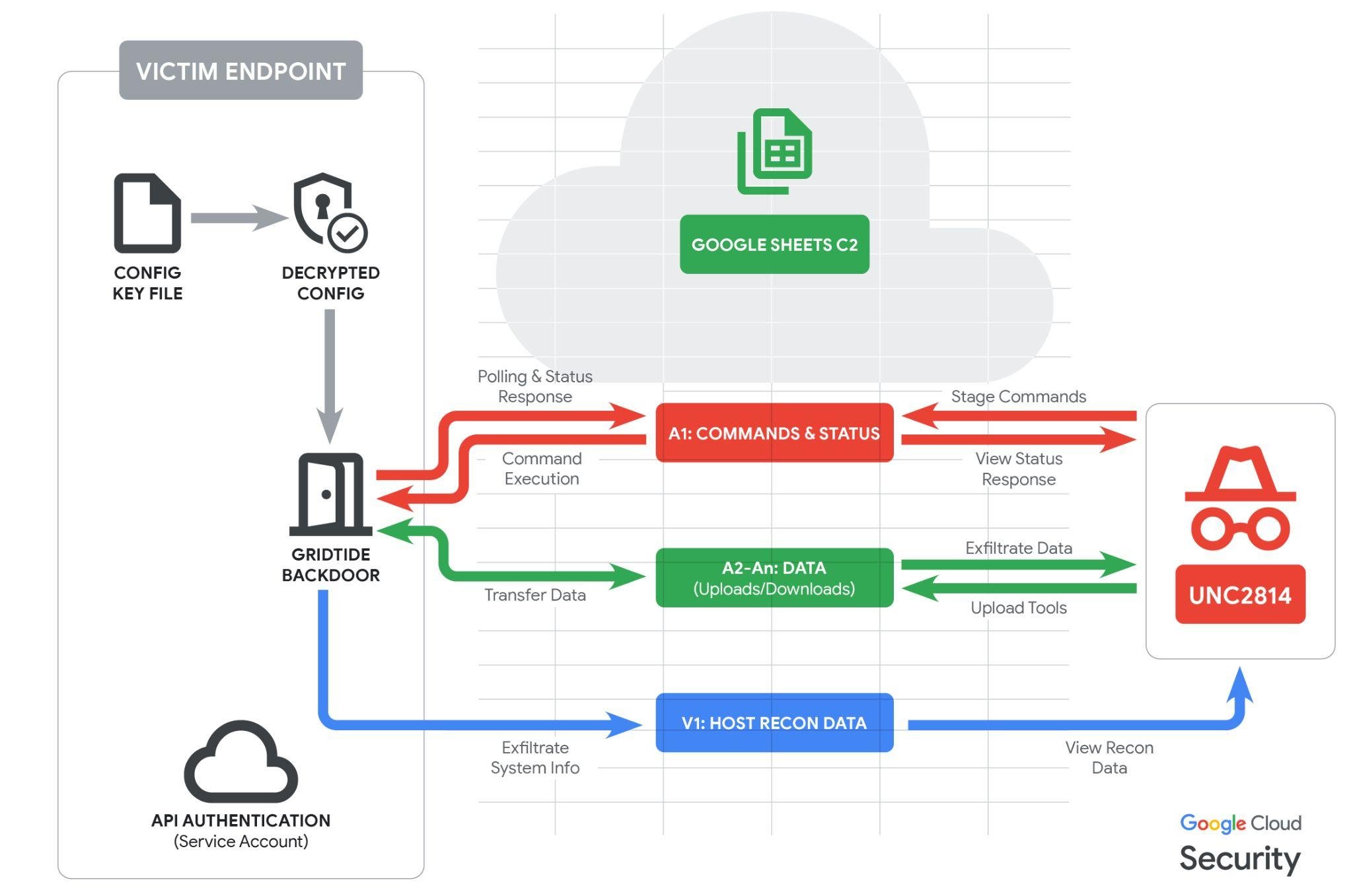
Mandiant’s investigation uncovered a new C-based backdoor, dubbed GRIDTIDE, which uses Google Sheets as its command-and-control (C2) channel.
Important to highlight that UNC2814 has no observed overlaps with activity publicly reported as “Salt Typhoon,” and targets different victims globally using distinct tactics, techniques, and procedures (TTPs).
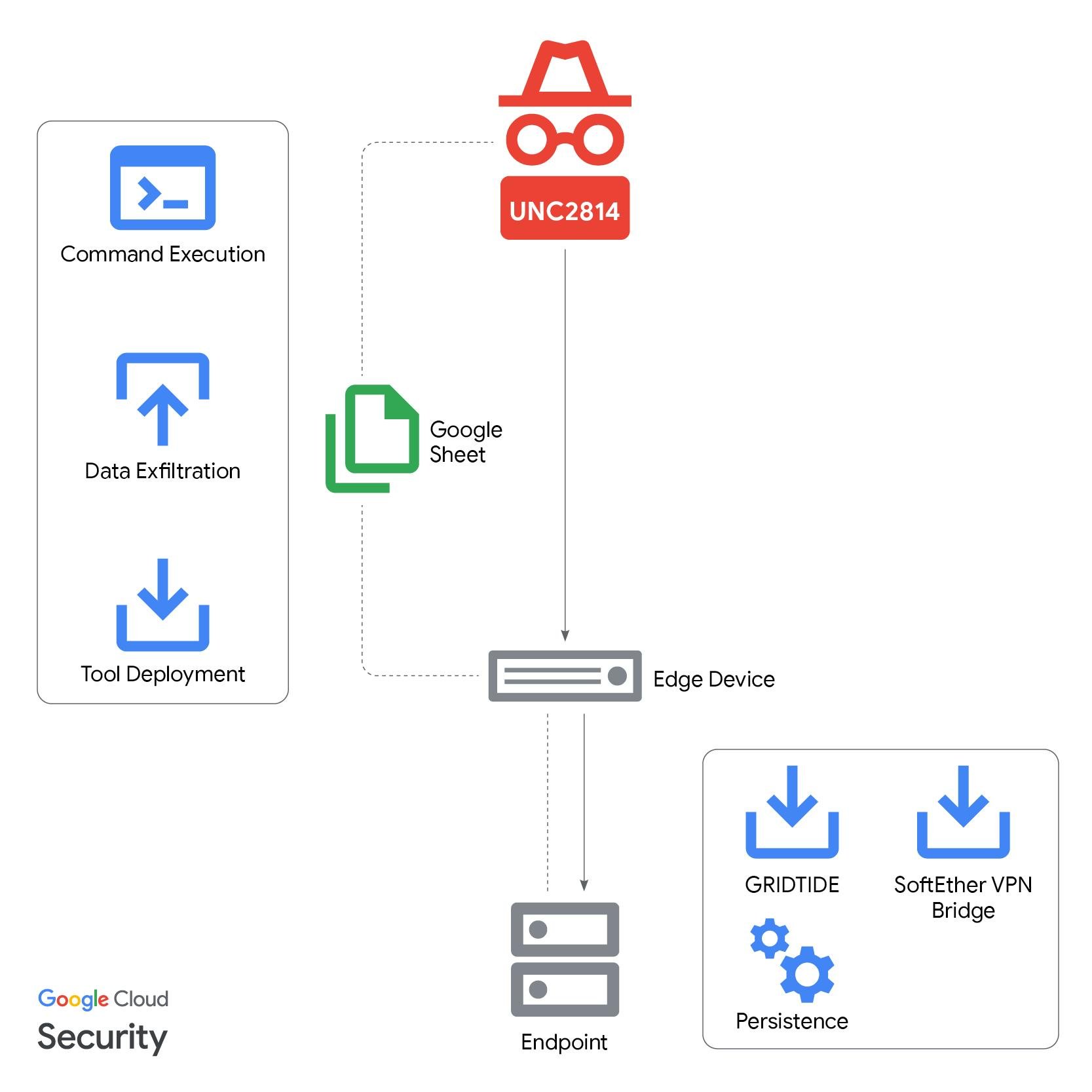
Instead of exploiting a vulnerability, the attackers abused legitimate Google Sheets API calls to blend malicious C2 traffic with normal cloud activity, making detection far more difficult.
GRIDTIDE can execute arbitrary shell commands, upload and download files, and hides its data exchanges inside routine-looking API requests to attacker-controlled spreadsheets.
To operate, GRIDTIDE relies on a 16-byte cryptographic key stored on the host, which it uses to decrypt Google Drive configuration data, including a Google service account, spreadsheet ID, and private keys.
The malware periodically polls specific spreadsheet cells for commands, writes the results back into the sheet, and uses cell ranges to exfiltrate data in small chunks to avoid raising suspicion.
The campaign often begins with the compromise of internet-facing systems, as UNC2814 has a track record of exploiting vulnerable web servers and edge devices for initial access.
Analysts observed a malicious binary “xapt” executing with root privileges on a Linux server, performing reconnaissance, then establishing persistence for GRIDTIDE via a systemd service.
Encoding variant replaces standard Base64 characters (+ and /) with alternatives (- and _).
The attackers used SSH and service accounts to move laterally, deployed SoftEther VPN Bridge for encrypted outbound connectivity, and then dropped GRIDTIDE on systems storing large volumes of personally identifiable information (PII).
The compromised data included full names, phone numbers, dates and places of birth, and national identity numbers, aligning with long-term surveillance and tracking objectives typical of PRC-linked cyber espionage.
Similar historic campaigns against telecoms have been used to access call detail records and SMS messages, and to abuse lawful intercept systems to monitor dissidents, activists, and strategic targets.
Google’s disruption actions
To break the campaign, GTIG and partners executed coordinated takedown measures against UNC2814’s cloud and network footprint.
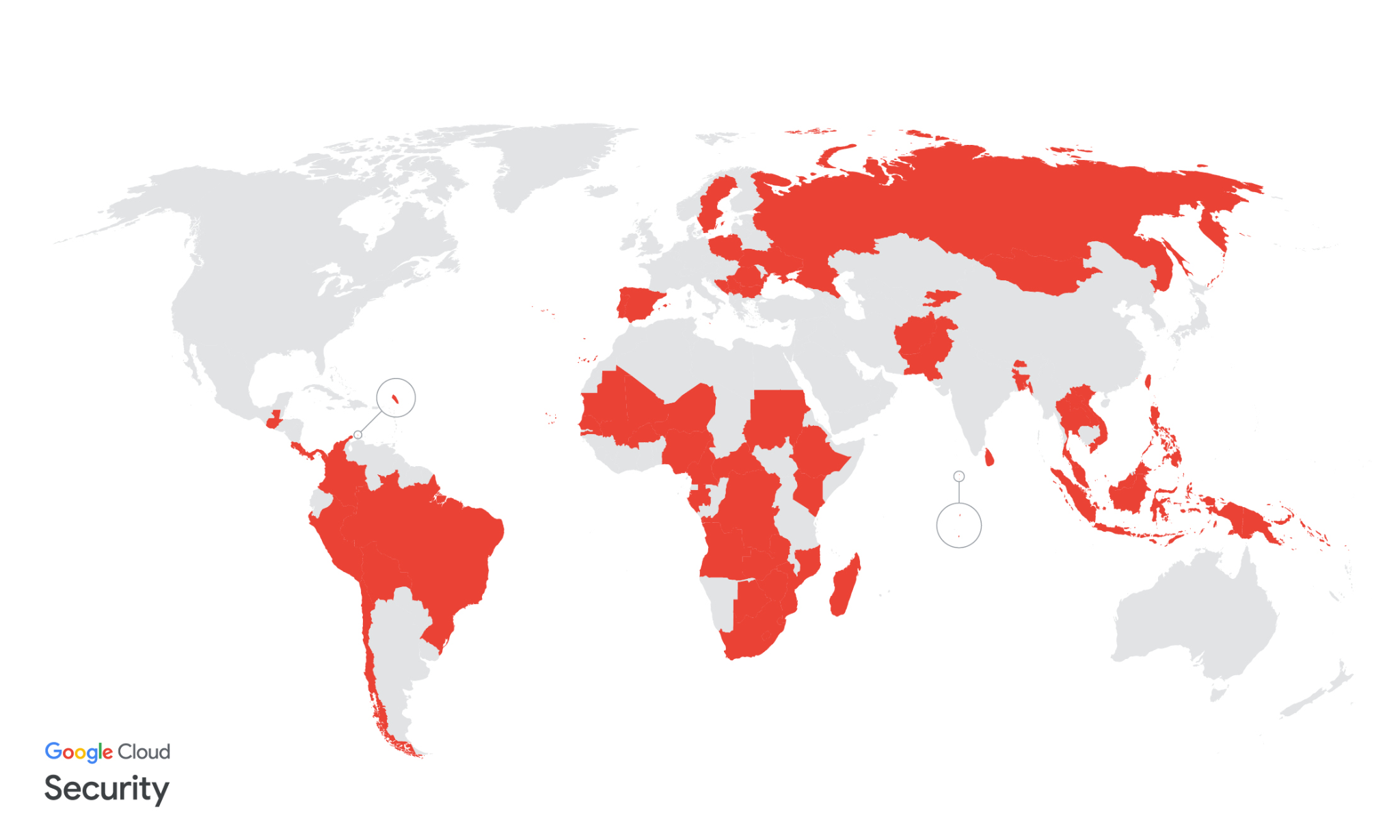
GTIG confirmed 53 intrusions by UNC2814 in 42 total nations globally, and identified suspected targeting in at least 20 other nations. This prolific scope is likely the result of a decade of concentrated effort.
They terminated all Google Cloud projects controlled by the attackers, cutting off GRIDTIDE’s persistent access to already compromised environments.
Investigators also identified and disabled all known UNC2814 infrastructure, including sinkholing both current and historical domains associated with the group’s operations.
Google and its partners further disabled attacker-controlled accounts, revoked access to Google Sheets API calls used for C2, and shut down all related cloud-resident C2 projects.
A set of detection signatures tied to UNC2814 infrastructure active since at least 2023 has been released to help defenders identify and evict the threat from their networks.
Affected organizations have received direct victim notifications and support, while GTIG warns that UNC2814 is likely to attempt rebuilding its global espionage infrastructure using fresh tooling and new cloud resources.
Indicators of Compromise (IOCs)
| Artifact | Description | Hash (SHA256) |
| xapt | GRIDTIDE | ce36a5fc44cbd7de947130b67be9e732a7b4086fb1df98a5afd724087c973b47 |
| xapt.cfg | Key file used by GRIDTIDE to decrypt its Google Drive configuration. | 01fc3bd5a78cd59255a867ffb3dfdd6e0b7713ee90098ea96cc01c640c6495eb |
| xapt.service | Malicious systemd service file created for GRIDTIDE persistence. | eb08c840f4c95e2fa5eff05e5f922f86c766f5368a63476f046b2b9dbffc2033 |
| hamcore.se2 | SoftEtherVPN Bridge component. | 4eb994b816a1a24cf97bfd7551d00fe14b810859170dbf15180d39e05cd7c0f9 |
| fire | SoftEtherVPN Bridge component (renamed from vmlog). Extracted from update.tar.gz. | 4eb994b816a1a24cf97bfd7551d00fe14b810859170dbf15180d39e05cd7c0f9 |
| vpn_bridge.config | SoftEtherVPN Bridge configuration. | 669917bad46a57e5f2de037f8ec200a44fb579d723af3e2f1be1e8479a267966 |
| apt.tar.gz | Archive downloaded from 130.94.6[.]228. Contained GRIDTIDE. | N/A |
| update.tar.gz | Additional archive downloaded. Contained vmlog (renamed to fire), a SoftEtherVPN Bridge component. | N/A |
| amp.tar.gz | Additional archive downloaded. Contained hamcore.se2, a SoftEtherVPN Bridge component. | N/A |
| pmp | GRIDTIDE variant. | N/A |
| pmp.cfg | GRIDTIDE variant key file. | N/A |